Description
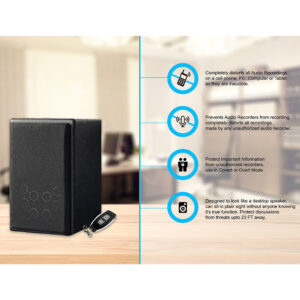
BH04PRO – Event Logging TSCM Detector – Memorize RF Threats
BH04 PRO is a professional modern detector with Event Logging capabilities.
Information Leakage detection can no longer depend on Live Scanning to sterilize Information Leakage threats.
Modern threats are designed to transmit information at irregular hours and remain in sleep mode for 95% of the time.
Event logging TSCM Detectors are the solution to modern informational leakage threats.
- Detection of 2G/3G/4G/5G Signals
- Detection of DECT/Bluetooth/GSM/WLAN/WIFI/GPS
- 3 Operation Modes: Search, Oscillograph, Security
- Background Subtraction Function
- 4 Banks of Memory 2,000 signals per Bank
- PDF Reporting – PC/MAC/Linux Compatible
- Acoustic Indication
- Probing Signal
- Antenna 1 – Frequency Range 10-2400 MHz
- Antenna 2 – Frequency Range 2400-8000 MHz (High Speed Channel)
- Dynamic Range – Up to 70 db
- High Sensitivity up to: -70 dBm (ANT 1) -50 dBm (ANT 2)
- Built in Frequency Meter – TURBO Frequency Identification
- Overwatch RF Monitoring Protocols – Security Mode
The BH04PRO is a professional TSCM detector with excellent performance during Live Sweeps and a constant monitoring mode which can proactively detect threats such as unauthorized eaves dropping devices.
Extremely effective tool for combatting information leakage, built to tackle sophisticated threats which utilize the internet of things – IOT.
BH04PRO has two independent search channels with separate Antennas and a built-in frequency meter which can report and identify frequencies extremely quickly.
The BH04PRO frequency meter is ideal for professionals, a TSCM sweep can sometimes be a time sensitive matter, the reporting and identification of frequencies can quickly give a Security professional key insights into the locations radio environment and certain frequencies may immediately be identified as rogue transmissions.
Example: If a TSCM sweep is being conducted, users have the ability to isolate all transmissions that are WIFI based, if the frequency meter still detects a WIFI signal, this would be an unauthorized transmission. A Threat.
The same isolation method method can be used for all frequencies that BH04PRO can detect – 2G/3G/4G/5G/DECT/Bluetooth/GSM/WLAN/WIFI/GPS
Operating in Live Environments
Sometimes sterilizing an environment is not possible. In an active environment where transmissions are critical to an organizations ability to be operational, BH04 PRO can still be used by using the Background Subtraction function.
Background subtraction is important in surveys where the location may be close to something like a cell tower operating at 900 MHz, the devices’ ability to memorize and while list specific transmissions, means you can rely on the device to detect actual threats and remember authorized transmissions.
Detection of Burst Signals
There are now more and more instances where modern threats being used to steal information are being configured to collect data such as audio files.
Such devices are normally activated based on sound or remotely activated devices; such systems can be set to transmit the data at a specific time via Wi-Fi/Data Plan etc.
These types of unauthorized devices are sometimes known as store and forward systems; capturing information and storing it until it is safe to transmit. Also known as Burst signals.
These types of unauthorized eavesdropping devices can collect data for long periods and then transmit them in just a few minutes. If such a device is used correctly, the system would be set to transmit data at a time when transmission will be least likely to be detected, transmission of data could take place out of normal office hours, to avoid detection.
These types of systems only need to be active for a few minutes to transmit the information and can then revert to sleep mode until sound is detected or the device is remotely activated.
Security Mode – Overwatch Monitoring System
Due to these technological advancements, systems like the BH04PRO are equipped with Security mode so they can be left in a location for constant monitoring of that location around the clock.
Activating the Security Mode on BH04PRO and leaving it in a high value location gives security professionals the ability to monitor the radio environment and identify potential rogue transmissions quickly.
Event Logging & Activity Reports
Users can easily view the activity report by connecting BH04PRO to a PC/Mac/Linux computer and generating PDF reports which can show you all frequency events occurring throughout the time the device was monitoring the location.
The report can identify each transmission by Frequency type, the time of transmission, and the length of time it was transmitting as well as the power level of the transmission.
Security Mode Activity monitoring on BH04PRO can store up to 2,000 signals per memory bank, there are 4 memory banks inside BH04PRO.
The Internet of Things – IOT
The Internet of Things (IOT) has made life easier and more convenient but mainstream use of IOT enables cybercrime and information leakage is fast becoming the biggest threat.
Modern IOT threats make live TSCM sweeps redundant as the sole method of detection, IOT threats can be remotely configured and scheduled to transmit data outside normal hours, making them very difficult to detect.
Example:
Corporate client has a highly sensitive meeting and requests a sweep of the room prior to the meeting commencing on the day of the meeting. Whilst you can sweep the room for live threats and use tools on the BH04PRO such as audio modulation to sniff out some inactive threats, digital devices which are set to record at a specific time, may not be detected due to them not being activated during the sweep, they may be in sleep mode, awaiting remote activation or even configured to record only at specific times.
Understanding the locations authorized RF transmissions layout round the clock allows corporate security professionals to continually monitor their high value locations and ensure areas are sterilized from unauthorized transmissions.
Activity Reporting
Reading the Activity report is simple. The date, time, and frequency are all recorded, and transmission readings are likely to be minimal providing the correct configurations were made to the environment by either using configuring Security mode to memorize the authorized frequencies layout.
Live Protection for Environments which need constant monitoring – Overwatch Protocols
Another great use for the Security mode is when sensitive meetings are taking place.
If no electronic devices are permitted in the meeting to minimize information leakage risk, the BH04PRO can be placed in the meeting room and immediately report any threats that may enter the room.
Also ideal for locations where devices like Cell Phones are not permitted. Use the BH04PRO for constant monitoring of high priority locations.
Advanced Functions paired with Ease of Use
BH04 is an advanced system but very easy to operate.
The onboard Frequency counter makes it very easy to identify RF transmissions very quickly.
The ability to not only detect but identify the transmission gives users the maximum discoverability with super-fast detection speed.
Excellent system for live TSCM sweeping but with the added function of Security mode monitoring for around the clock protection.
Using Security mode in a high value environment for a prolonged period helps reduce the threat of store and forward devices (burst signals).
In the age of IOT accounting for burst signals which may be transmitting data when locations are closed is a primary threat that should always be factored into a professional TSCM Sweep.
Specifications –PBN-BH04PRO
| Frequency range |
|
| Sensitivity of frequency meter | Up to -50 dBm |
| Sensitivity |
|
| Dynamic range |
|
| Operation modes | Search, oscillograph, protection |
| Power consumption | Up to 0.6 W |
| Power | 3.5 – 4.2V Li-Pol battery (could be charged by 110/220V mains or by 5V 1A power adapter) |
| Dimensions | 130 х 80 х 16 mm (5.0 x 3.0 x 0.6 in) |
| Weight | 200 g (7.0 oz) |
What’sIncluded with the BH04 PRO
- RF signal detector PBNBH04PRO
- Antenna 10-2400 MHz (ANT1);
- Antenna 2400-8000 MHz (ANT2);
- Power adapter;
- Mini-USB cord;
- Headphones;
- English Manual;
- Warranty certificate;
- Foam Cushioned Packaging/Box.TSCM Professionals
Excellent system for sweeping; small form factor and advanced functionality – TSCM professionals can develop their service offerings by supplying key clients with this system as a constant security measure which can be used as a first port of call in the event a sweep needs to be conducted.
Excellent way to have a continual monitoring system in place, a proactive measure against unauthorized eavesdropping devices.
TSCM professionals can also request their key clients email them the reports for professional review purposes, tightening their security protocols for high value locations.
Corporate Security Professionals
As detailed above, the BH04PRO provides a constant monitoring platform to protect sensitive environments 24/7.
This form of protection is sometimes known as OVER WATCH, being able to monitor, record and report environments for potential threats in real time ensures any advanced investigations have a strong understanding of the RF environment.
The ease of sharing the PDF reports ensures TSCM professionals can gain a strong understanding of the environment before they enter the location.
Secure Environments
Locations such as Prisons can clearly benefit from this type of system. The small form factor and fast detection capabilities can be used in many scenarios.
Checking incoming prison inmates, checking visitors prior to visiting inmates, performing audits for unauthorized digital contraband such as cell phones, etc.
Prisons are an obvious place for this type of solution but more and more with the advancement of IOT, tools like BH04PRO can play a big part in protecting other environments such as data centers and server rooms where a rogue transmission could create immediate havoc.
Using the Security Mode function in a high value location allows BH04PRO to memorize the RF layout and detect only unauthorized RF transmissions, ideal for data centers which need to be protected at all costs.
Vehicle inspections
BH04 can be used to monitor a vehicle for burst signals such as a GPS tracker.
Harassment and Stalking Victims
More and more we are learning about new methods people are using to exert control over victims of crimes such as stalking and harassment, the BH04 PRO has been used by multiple victims of harassment and stalking to sniff our rogue transmissions that are capturing and reporting information on a victim’s whereabouts and activities. In many cases the threats were left at a person’s home or the criminal gained access to the home and planted the device, for long term monitoring of a victim’s day to day activities.
Requirements:
Activity Logging can be viewed as a PDF report by connecting device to PC/MAC/Linux
-
FAQ
Q: Can this TSCM Detector detect 5G signals?
A: Yes, this TSCM detector detects RF signals across the following frequencies:
Detection of 2G/3G/4G/5G Signals
Detection of DECT/Bluetooth/GSM/WLAN/WIFI/GPSQ: How do I monitor a room for a pro longed period?
A: Set the device to Security mode, ensure all transmissions are isolated or ensure you set the device to remember any transmissions which are authorized.
Leave the device in the high value location for up to 1-3 days and monitor the RF environment.
Plug the device into any PC/MAC/Linux Computer and generate an RF activity report. The report will show you the time, type of transmission and how long the transmission was transmitting for.
Q: Can this device detect burst signals?
A: Yes, this device’s primary function is to detect and record RF activities, whilst this system can be used to perform live sweeps it has the advanced memory banks on board for pro-longed monitoring which can be very helpful for the detection of burst signals.
Q: Is TSCM now a Cyber Security task?
A: Information leakage can be a concern for both cyber security and Technical Surveillance Countermeasures (TSCM).
Cyber security deals with protecting computer systems, networks, and data from unauthorized access, use, disclosure, disruption, modification, or destruction. Information leakage in the context of cyber security refers to the unauthorized disclosure of sensitive or confidential information through electronic means such as hacking, phishing, or malware attacks, any of these attacks can originate as a result of an unauthorized eaves dropping device being placed inside an organization.TSCM is the practice of identifying and mitigating threats posed by eavesdropping devices or other forms of technical surveillance. TSCM focuses on protecting information from physical breaches, such as audio or video recording devices, hidden cameras, and wiretaps.
In summary, while information leakage can be a concern for both cyber security and TSCM, the approach to addressing it may differ depending on the source of the threat.
Cyber security focuses on protecting against electronic breaches, while TSCM focuses on physical breaches.
Whilst there is a distinction between the two types of security, the need to ensure co-operation between departments has grown exponentially because of the advancement and sophistication of unauthorized threats penetrating high value locations within organizations.